Member-only story
How To Connect a Custom Power Apps Connector To Azure API Management
I recently embarked on a journey with my colleague Lukman Balunywa to uncover all the details involved in connecting a custom Power Apps connector to an Azure APIM instance. This blog post is the result of this research which will help you navigate some of the pitfalls you may face while attempting to connect these two services together.
Before we start discussing the details behind the integration between the two services it’s important to start by understanding the APIM environment that is being exposed. The APIM instance exposes a logic app backend. The API on the APIM frontend is protected by both an Azure AD OAuth 2.0 token as well as an APIM product subscription key. Thus, the PowerApps connector has to provide both of these security mechanisms when making the call.
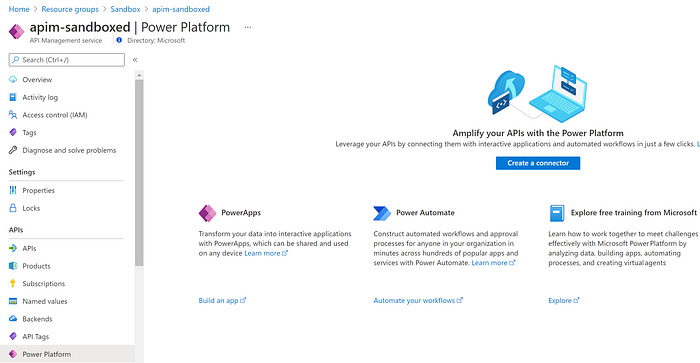
Currently there are several ways in which you can create the custom PowerApps connector from the Azure APIM side. The most obvious way is the new PowerApps blade which allows you to create a connector as shown in Figure 1. Another option is to export the API in OpenAPI v2 (JSON) format and later import it on the PowerApps side as shown in Figure 2 and Figure 3 respectively.
Note: We noticed that integrated option within APIM doesn’t allow providing OAuth scopes. You can go back and provide that from the PowerApps side after the custom connector gets created as shown in Figure 4.
Note: At the time of writing this post PowerApps didn’t support OpenAPI v3.

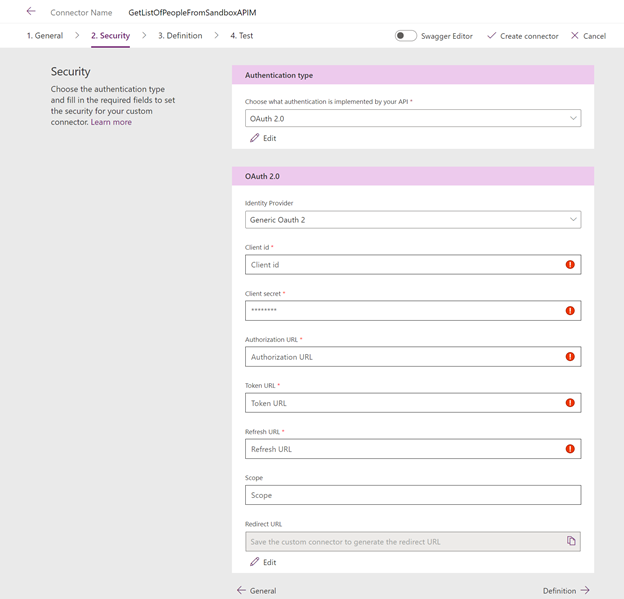
Its worth noting here that the assumption is that the application registration on the Azure AD side has already been created. The only thing that needs to be updated on the Azure AD side after creating the custom connector is the redirect URI. As shown in Figures 5 and 6 the PowerApps custom connector provides a Redirect URI that needs to be provided on the Azure AD application registration side respectively.
